You are going to be spending proportionately more of your IT budget on security than you have previously spent or ever wanted to spend. Why? Because you and everyone else on this planet is engaged in the still early stages of an escalating information arms race, that, while you didn’t ask for it, neither can you avoid. This escalation is being driven by two recent IT phenomena: exploding connectivity and transparency.
An article in the March 2015 edition of Scientific American by Daniel Dennett, professor of cognitive science at Tufts, and Deb Roy, director of the Laboratory for Social Machines at MIT, expounds on this idea by linking it in a wonderful analogy to a hypothesis regarding the Cambrian explosion which occurred on this planet 542 million years ago.
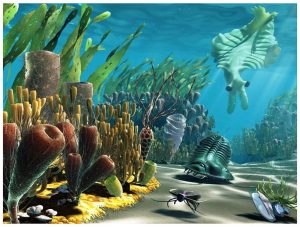 The Cambrian explosion saw, in a mere geological instant, life on Earth move from single to multicellular organisms, and with it the emergence of all the varied body plans (phyla) we see today, from arthropods (lobsters) to mollusks (clams) to echinoderms (starfish) to chordates (sharks). Prior to this, life had existed on Earth for over 3 billion years as nothing more complex than single-celled bacteria or algae, and then, in the blink of an eye over a span of only a few tens of millions of years, 34 of the 35 separate animal phyla arose from the relatively simple amoeba-like creatures of the day. Why the sudden change?
The Cambrian explosion saw, in a mere geological instant, life on Earth move from single to multicellular organisms, and with it the emergence of all the varied body plans (phyla) we see today, from arthropods (lobsters) to mollusks (clams) to echinoderms (starfish) to chordates (sharks). Prior to this, life had existed on Earth for over 3 billion years as nothing more complex than single-celled bacteria or algae, and then, in the blink of an eye over a span of only a few tens of millions of years, 34 of the 35 separate animal phyla arose from the relatively simple amoeba-like creatures of the day. Why the sudden change?
Oxford zoologist Andrew Parker posits (“In the Blink of an Eye”) a new and compelling hypothesis for the Cambrian trigger: light. He proposes that around 550 million years ago the chemistry of the sea changed such that the oceans now became much more transparent to light. The chain of reasoning would go roughly as follows:
- With more light available, eyes developed (multiple times) to exploit the visual medium and make hunting more effective.
- Hunting put a premium on mobility, thus an initial explosion of multicellular, mobile body types.
- Predation then put pressure on developing effective defensive countermeasures, such as calcium carbonate shells.
And thus the evolutionary arms race was on, with rapid improvements in vision, locomotion, claws, shells, camouflage and eventually, nervous systems, to coordinate everything.
The Internet, connectivity, social media and mobile/smart devices have had the same effect on our information environment – they have made it transparent – to friend and foe alike. We have had information, and even information overload, for some time now, beginning with the printing press and extending from the telegraph, telephone and television into the Computer Age of the late 20th century, but until recently it was a disconnected, opaque world. Now, however, it’s a game of information hide-and-seek.
The first predator to evolve out of the muck and slime of the pre-IoT information world was the Hacker, from the phylum ‘programmer’. The hacker’s further evolution into a complex socially networked creature has resulted in another new phylum – CaaS, or Crime as a Service. From a Europol report: “A service-based criminal industry is developing, in which specialists in the virtual underground economy develop products and services for use by other criminals. This 'Crime-as-a-Service' business model drives innovation and sophistication [i.e. evolution].”
Depending on your business, garden variety criminals may be the least of your worries. As James Lewis from the Center for Strategic and International Studies puts it, "Criminals are opportunistic - they just want to make money. But government-sponsored hackers [like those who attacked Sony]will just keep trying and won't give up. The politically motivated can be vindictive - this was not done for the money."
An interesting related perspective comes from Joel Brenner, former senior director at the NSA – the concept of the “half-life of secrets”. To quote Brenner, “Very few things will be secret anymore, and those which are kept secret won’t stay secret very long. The real goal in security now is to retard the degradation of half-lives of secrets.”
This is not good news for the commercial business entity, where “retarding the degradation” seems inadequate and underwhelming as a strategy for protecting customer data. But if this truly does represent the new reality, not only do you have to bake security into your products and processes from the start, you have to assume it has a quantifiable half-life, that you are going to get hacked eventually, and that you will require contingency plans not for "if", but for "when".
A robust cybersecurity strategy aimed at extending that half-life would likely include these analytically-supported aspects of security intelligence:
- Fraud management, to detect and prevent fraud, such as improper payments
- Threat identification including data exploration and behavioral analytics
- Real-time data monitoring and situational awareness
- Real-time response capabilities such as event management
- Robust operational risk management and enterprise governance to include security
- Machine learning - The evolution of analytic models throughout the analytic life cycle, ensuring that as your adversaries get more sophisticated, so do your detection methods.
Perhaps not as threatening but equally significant to your business is how you manage and react to the new transparency of social media. Are you at least monitoring the environment? Have your marketing and PR operations evolved to deal efficiently and effectively with customer / influencer social conversations, comments, opinions, ratings, review, rumors and other viral impacts to your product and corporate reputation?
No need, however, to only see the information glass as half empty. Don’t forget that this Cambrian analogy also has an “explosion” component to it. Just as these early Cambrian organisms evolved into the vast complexity of life we see around us today, so too does the connectivity and transparency of our information age portend a future of yet undiscovered business models, strategies and value creation opportunities.
It is worth noting that, with one or two exceptions, no new animal phyla have appeared on this planet since the end of the Cambrian – no new body plans, no significantly new organism forms in over 500 million years. If our current stage in the Information Age represents an analogous period in economic history, will you be ready to take advantage of the unique opportunity this new transparency holds for business model diversification? The danger is that there is now a new way for businesses to go extinct via cyber-threats, but for those who can adapt, and adapt, and adapt, and adapt (i.e. evolve), there will be open economic / ecological niches everywhere awaiting your strategy for creating value.
