In May this year a great number of telecom operators gathered in Lisbon, the city of Fado, to discuss telecom fraud. Organized by the Communications Fraud Control Association (CFCA) and the Forum for International Irregular Network Access (FIINA), operators ranging from AT&T, Vodafone, Korea Telecom to Orange and Deutsche Telekom shed light on how old and newer forms of telecom fraud are detected and combatted.
As the Fado lyrics often deal with the life of the heart-broken and days past, telecom fraud nowadays deals with the whereabouts of criminals, increasingly organized crime. And as telecom fraud becomes more organized and sophisticated, so need the tools and methods for detecting and combatting current and future practices.
Too often, telecom organizations are working in a reactive approach where responsible fraud managers act as a plumber: they look out for anomalies in traffic, literally the ‘odd ones out’ - traffic to national and international suspect destinations and number ranges and traffic coming from new, potentially ‘risky’ applicants – before they try to repair the leaks. This is typically done by patching the firewall, maintaining static “black lists” and looking for illegal simboxes.
But looking at the individual cases, do they see the bigger picture? Aren’t there too many ‘false positives’ clogging up too many scarce resources. Are relations between fraud cases and fraudsters visible? And what about the fraud schemes that are not solely or not at all call related? The possible connections between external fraudsters and internal employees? Supplier fraud? Subscription fraud? And the hidden cases? The false negatives, the cases that stay below the radar?
Telecom Fraud is big business
The communications industry ranks in the top 5 industries most threatened by economic crime according to a recent PWC survey (Global Economic Crime Survey 2016). It’s ahead of sectors such as insurance, manufacturing, energies, utilities and construction, and ranks straight after banking, public, media and transport/logistics.
Interestingly a great number of operators are eyeing up banking and media/entertainment companies and broaden their activities, thereby increasing their exposure to economic crime, fraud, money laundering et cetera substantially. Currently operators lose a whopping 38 billion US dollar to fraud, according to last year’s CFCA survey. Top methods are typically (IP)PBX hacking, subscription application fraud, dealer fraud and subscription identity fraud.
Not only traditional telecom is affected: also cable/satellite/IP TV providers are targeted by fraudsters with unlawful card sharing and illegal streaming. Even in a small country as the Netherlands with 7.4 million households roughly EUR 14 million is lost annually due to illegal TV viewing, according to the Dutch cable association.
And as cybercrime has climbed up the ladder of fraud methods according to the PWC research, we can expect this to become a new category soon in telecoms as well. An example in case is a hack in the dealer system of a European carrier where prepaid cards were switched to postpaid, thereby enabling the fraudsters to run up high bills without paying for them. Calls were made to so-called International Revenue Share Fraud numbers, nowadays openly available and traded on the internet.

Kick-back and revenue share models enable all criminals involved, home and abroad, to take their unfair share from these scams, leaving customers and often operators to foot the bill. Sometimes internal resources can be implicated: employees committing unauthorized conversions from prepaid to postpaid in the HLR or suppressing billing Call Detail Records or even call agents implicated in unduly complaints.
A fresh KPMG research on fraudster profiles found that groups of fraudsters very often comprise people both inside and outside the company. Sixty-one percent of colluders are either not employees of the company, or are employees who work with people who aren’t. Some of them are former employees. This highlights the need for better third-party due diligence of such persons as vendors and customers.
Another fraud form, related to vendors (and customers) are VAT fraud, or so-called Missing Trader Intra-community (MTIC) fraud which is also prevalent in telecoms, especially regarding handsets and CPE. Also malware, enabled via unsolicited messages and installed on a mobile phone, can do the trick. With Voice over LTE (VoLTE) mobiles are even more exposed to fraud because signaling is implemented in the mobile OS instead of mobile-based broadband, as for 2G/3G telephony. Many of these vulnerabilities can then actually be exploited remotely through mobile malware.
Moreover, as the number of new, connected networks grow and the number of devices explode with the advent of the ‘Internet of Things’, new forms of economic crime will emerge. We already know of hacking connected ‘things’, whereby running up phone bills is only one part of the damage done. What about criminals hacking into your smart home, as your customer forgot to change the default password settings? Reputational and brand damage can be often much bigger.
Maybe operators, at least some, want to exude ‘security’ and ‘trust’ as part of their brand image and core values – just like banks do. And increasingly critical private and business customers expect their telecom provider to protect them from harm done.
Analytics coming to the rescue
Traditional, often rule-based investigations can only detect so-much of fraud. As KPMG concludes in its fraudster profiles report: “The key anti-fraud technology is data analytics, a tool that can sift through millions of transactions, looking for suspicious items. But only 3 percent used pro-active anti-fraud data analytics in detection of the fraudsters surveyed.”
Learn more about the analytics economy and how you can transform your organization into tomorrow’s telco by downloading this paper.
Data analytics can go much deeper, look beyond the obvious. Analytics is an encompassing and multidimensional field that uses a combination of mathematics, statistics, predictive modeling and machine-learning techniques to find meaningful patterns and knowledge in recorded data. This can be internal data, but also external data sources, such as Chamber of Commerce information, social media, or (IRFS) websites.
Adding powerful and cheap processing and storage methods, such as Hadoop, for analyzing increasing amounts of data and running sophisticated software algorithms – producing the fast insights needed to make fact-based decisions. By putting the science of numbers, data and analytical discovery to detect and combat fraud, we can find out if what we often assume or believe is really true. See hidden patterns. More specifically analytics can help with:
- Increase efficiency by reducing wasted time spend on investigating false-positive alerts. A sophisticated fraud scoring engine applies risk- and value-based scoring models to prioritize events before they go to investigators. With the time saved, investigators can work many times the number of cases and focus on higher-value networks. Moreover, the outcome of the investigation is sent back to the system in order to continuously increase the detection accuracy.
- Spot more suspicious activity by processing all data (not just a sample) through analytical models in batch or if needed in near-real time as data streams in. Also bringing in new, external data sources with structured and unstructured data (even text-analytics).
- Detect also first and third party fraud networks and crime rings that would otherwise be missed. Also automatically identify suspicious networked behavior in the data. Identify early risky applicants and transactions.
- Increase the collaboration between the fraud & marketing and finance/credit risk departments thanks to efficient customer screening and scoring. Without interfering with the customer journey, the analytical models can prevent losing money and high-end devices to fraudsters who should not become customers. Or use different offerings to different customers depending on their risk profile.
An encompassing fraud framework
One of the challenges for combating telecom fraud is dealing with its many forms - TM Forum has made a classification which, ideally, is tackled from one framework, instead of using different tools for different forms.
Combating telecom fraud is dealing with its many forms, ideally from one #fraud framework. #telecom Share on X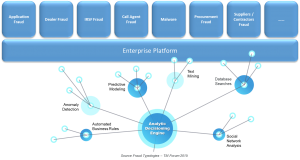
Most telecom operators have a classical Fraud Management System that mainly focuses on call related frauds such as IRSF, PBX and other frauds. When new fraud modus operandi become more important, the fraud investigators are often not able to detect these in time.
Therefore, it is important to have a Fraud Framework that enables you to cover all types of fraud in a flexible way and works as an Enterprise Platform. The usage of analytics is certainly a key factor in order to fire the alerts but there are also other layers within the framework that are equally important:
- Integration, quality and management of data: The telecom operators are facing a high volume of data internally (CDR, customer data, etc.) but should also leverage external data, structured (lists, demography statistics, etc.) and unstructured (social media information, web crawls, etc.). All this data should be brought together which will require a system that can access all these sources transparently and which can also handle the data cleansing in order to make sure that the data quality is optimal.
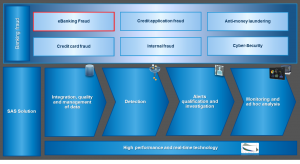
Figure 2. SAS® Fraud Framework - Detection: Using a hybrid analytical approach (combination of business rules, anomaly detection, predictive modeling and social network analysis) in a white-boxed approach will enable not only to detect all types of fraud but will also highly decrease the false positives whilst increasing the hit rate.
- Alerts qualification and investigation: Alerts should be shown in an understandable manner to the fraud investigators, giving them the opportunity to visualize and prioritize the alerts following their internal processes and needs. For each of the alerts, the investigator needs to clearly understand the reasons of the alerts in order to ease and shorten the investigation time and process. After investigation, the outcome will be sent back to the system in order to increase the detection logic (feedback loop).
- Monitoring and ad hoc analysis: the follow-up and pilotage of the fraud information can be used by the general management to determine the future fraud prevention approach but also to fine-tune long term strategies in different domains (fraud, marketing, risk, etc.).
- High performance and real-time technology: In order to avoid that fraud losses explode quickly, the fraud framework has to work (near) real time. This will also prevent that the fraud detection interferes in the customer journey of new and existing customers.
As a conclusion, it seems obvious that the telecom business is still very lucrative for fraudsters. Fraud losses are still not under control and the fraudsters continuously find new ways to increase their profit.
Nevertheless, the new technologies and the usage of advanced analytics can help the operators to stop this phenomenon. Other sectors such as the banking sector have already embraced these methodologies with success and although not obvious, there are a lot of best practices that could be copied and applied similarly to the telecom sector. But that is another story…
Learn more
In our digital world, where everything is available via the web, there is a whole new level of fraud. To understand how you can detect and combat emerging fraud methods, get inspired by this whitepaper, Fraud in Communications.
Matthieu Joosten is Telecom Industry Lead at SAS South West Europe
Frédéric Hennequin is Senior Solution Specialist Fraud at SAS Belux
